SCROLL DOWN
Rubrik Telemetry =
We utilized Rubrik telemetry in an effort to understand a typical organizations data estate and the risk realities.
Wakefield Research =
Perspectives from 1,600+ IT and security leaders
Rubrik Partners =
Research and guidance from two Rubrik partners




Contributing Organizations =
Research from respected cybersecurity organizations and institutions










FIRST
We're going to make the “risk math” easy:
What is the likelihood your data will be affected by an external entity

What is the risk resident in your data today

The impact that's likely to produce

Your decisions in response to the impacts

Risk Math
In your face big math!
SECOND
We're going to focus on data.
As a data security company, our strongest insights involve an organization's data—as opposed to its infrastructure or architecture—so we focus on risks in and to your data.
Specific Focus Areas
Let's be honest. You're busy. None of us have time for a full deep-dive on every aspect of data security. We intentionally narrowed this study to a few key topics:

Cloud.
The existence of commercially available clouds can now be measured in decades. Yet, confusion about cloud data security remains. The cloud is targeted with more frequency—and more success—than its on-premises counterparts. It also contains blind spots making them difficult to defend.

Ransomware.
Not too long ago, experts predicted ransomware's decline. It didn't really happen, and ransomware continues to wreak havoc on organizations of all kinds.

Healthcare.
With few exceptions, healthcare organizations produce and store more sensitive data and are subject to more regulatory scrutiny than other industries. A fringe benefit of the regulatory pressures on healthcare is more publicly available data to study.
THIRD
Who is this study for?

Intelligence should inform the right decision-makers, and risk decisions typically happen at the senior-leader level.

Our goal is to inform and aid these senior-leader discussions across business, cybersecurity, and IT functions.

By giving these decision-makers a common place to start from, they'll be better prepared to tackle risk together.
If a meteorologist tells you there's a 52% chance of rain in your area, they're not telling you definitively, "Yes, it will rain," or "No, it won't."
It would be nice if you only had to make these decisions once.
But... it just doesn't work that way.
Let's start with the external threats you should consider.
EB vs. BEPB
A reminder from the data nerds: When most of the world hears "data," they think of logical storage, also known as frontend storage. Those of us in the data business focus on backend storage. Rubrik takes the entirety of an organization's data and performs a number of different techniques—including deduplication and compression—to reduce the amount of frontend data to backend storage. We'll use backend storage throughout this journey.
How much is 42 EB?
Think about your healthcare record with all the forms, images (x-rays, MRIs, etc.), notes, and other data. If you're like most people, your healthcare record is about 80 MB.
If Rubrik's 42 EB of protected data consisted of nothing but healthcare records, it would be the equivalent of five healthcare records for every one of the 117 billion people who lived on earth for all of humanity's history. It's like…a lot.
WAKEFIELD RESEARCH
We partnered with Wakefield Research to conduct a study that gathered additional insights from both IT and security leaders. This data supplements our Rubrik telemetry to give us insight into both the leaders' point of view and what they see on the ground. No Rubrik clients are included in this dataset to be as objective as possible.
1,600+ IT and security leaders
10 countries
50%+ CIOs or CISOs
Rubrik Partners
We leveraged datasets and received guidance from two Rubrik partners in ongoing efforts to improve data resiliency.

Microsoft provided data from the 2023 Microsoft Digital Defense Report, specifically data exfiltration rates and resiliency recommendations.

Aon provided data from the 2023 Aon Cyber Resilience Report , specifically data backup realities and post-intrusion outcomes.
Contributing Organizations
Rubrik included key data from various organizations with unique visibility compared to Rubrik telemetry in efforts to provide as objective a view as possible.

Mandiant provided dwell times observed in its incident response/MDR events across 2023.

Palo Alto Networks Unit 42 provided findings on ransomware demands and payments from their incident response/MDR events across 2023.

Proofpoint provided information on cloud targeting based on their 2023 Human Factors Threat Report.

Recorded Future provided publicly reported ransomware trends across 2023.

The University of Minnesota Twin Cities - School of Public Health provided ransomware impacts on public health institutions based on their research “Hacked to Pieces? The Effects of Ransomware Attacks on Hospitals and Patients,” which is published and currently undergoing final peer review.
Let's start with how we think about risk.
Let's start with a basic question:
Are attackers likely to target my data?
Nobody can tell you with 100% certainty if you'll be hit with a cyberattack, but we can tell you what happened to your peers last year.
Almost all your peers dealt with cyberattacks about every other week
Almost all your peers dealt with cyberattacks about every other week
Here's what last year looked like across IT and security leaders:
94%
of IT and security leaders reported their organizations experienced a significant cyberattack last year.
30
The average frequency was 30 malicious events brought to senior leaders' attention across 2023.
93%
of external organizations conducted a formal data loss notification to a governing organization.
Cyberattacks are far more likely than physical theft or fire.
To put the likelihood of cyberattacks into perspective, a European insurance company compared cyberattacks to traditional threats in the same timeframe and found:
67%
Organizations are 67% more likely to experience a cyberattack than physical theft.
5x
Organizations are five times more likely to experience a cyberattack than a fire.
20%
of organizations do not know what actions to take in the event of a cyberattack.
Cyberattacks are far more likely than physical theft or fire.
Attackers are comfortable targeting hybrid environments.
Attackers are comfortable targeting hybrid environments.
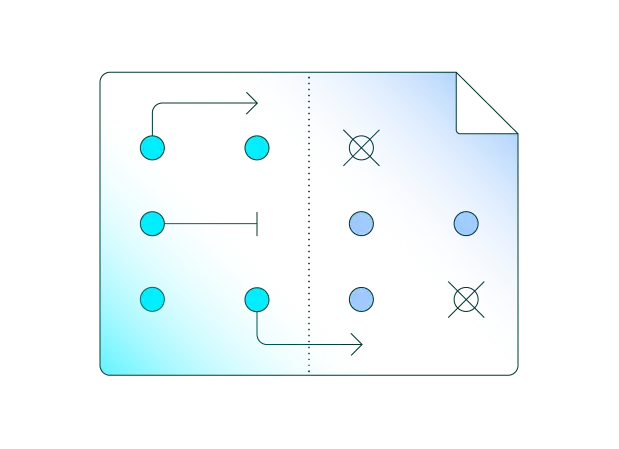
So if you're likely to be targeted, it's useful to understand where and what is likely to happen. Of the 94% of external organizations victimized in a cyberattack, many were attacked across multiple environment types:
67% Saas
66% Cloud
51% On-Premises
And here's some perspective on the two most common types of attacks in these environments:
38% of these organizations had at least one data breach from a cyberattack.
33% of these victims endured at least one ransomware attack.
Almost all cloud tenants were targeted, and 2 out of 3 were compromised in 2023.
We didn't just find this in our own research. Proofpoint reported:
94% of cloud tenants were targeted every month last year.
62% of targeted cloud tenants were successfully compromised.
Almost all cloud tenants were targeted, and 2 out of 3 were compromised in 2023.
Attackers have access to your data for days before being found.
Attackers have access to your data for days before being found.
Mandiant measures dwell time as the number of days an attacker is present in a victim's environment before detection.
10 DAYS The global median dwell time across all events was 10 days last year.
5 DAYS The global median dwell time for a ransomware event is 5 days.
THE GOOD NEWS
these are the shortest dwell times ever observed by Mandiant.
THE BAD NEWS
this still represents a significant length of time for malicious actors to accomplish their goals.
358 reported ransomware attacks against healthcare (46% increase YoY).
4,399 reported attacks across all industries (70% increase YoY).